iPAS: Our Platform
A persistent, memory-driven security lifecycle.
How it Works
Traditional security tooling behaves like a stateless scanner: it runs, produces output, and forgets. iPAS is designed differently. It behaves like a persistent attacker with memory — because real attackers don't start from zero every time.
What "memory" means in practice: we don't charge you to rediscover the same assets twice. We build on prior intelligence, prior exploit paths, and prior remediation history. Each engagement begins more informed than the last. That's how you reduce repeat work, shorten cycles, and keep pressure on what actually matters.
Scapien mirrors real attacker logic through a structured sequence:
Recon → Explore → Prioritize → Attack → Research → Publish
Each phase feeds the next. When a new engagement is scheduled, the process resumes with accumulated knowledge — not from scratch.
Walk through your environment priorities with a Scapien operator. No sales cycle required.

The iPAS Lifecycle
The lifecycle begins with reconnaissance focused on observation rather than interaction. Passive techniques allow Scapien to understand what exists in the environment without triggering endpoint detection, intrusion detection, or availability risks. This phase builds initial asset awareness and behavioral baselines. Think of this like attacker dwell time: a real attacker sits quietly, watches how the environment behaves, notices what talks to what, and learns where the high-value paths likely are — before touching anything noisy. Unlike predefined breach simulations, reconnaissance begins with environmental awareness — not assumption.
Exploration converts observation into structured hypotheses. If an asset is observed communicating in a certain way, or running a specific service, Scapien formulates targeted questions: What version is this? Is authentication enforced? Are there known weaknesses? Exploration is selective and bounded. It is designed to answer high-value questions efficiently — not to generate noise for its own sake. The goal is to separate "interesting" from "irrelevant" quickly and focus attention where meaningful exploit paths may exist.
Findings and observations are not treated equally. Prioritization incorporates asset criticality, data sensitivity, exposure context, and exploitability. This ensures effort focuses on paths that represent meaningful security risk — and ultimately business impact. For resource-constrained teams, this is the difference between drowning in vulnerability volume and maintaining a defensible queue. The platform surfaces validated, ranked security risks in a clear order — so remediation can move forward with confidence.
Where justified, Scapien performs controlled exploit validation to confirm whether a potential weakness is actually exploitable in the customer environment. Exploitation is evidence-driven and bounded by safety, authorization, and rules of engagement. This replaces "the scanner said so" with defensible proof. Findings are validated before they become operational work.
Research captures and enriches evidence — screenshots, command output, credential proof, and data access artifacts — to clearly demonstrate impact. Just as important, this is where remediation is understood. We translate what we observed into how to fix it safely in your environment, what dependencies matter, what common false fixes look like, and what closure criteria should be. This is how you shorten time-to-remediate (TTR): not by delivering opaque vulnerability data, but by providing specific, researched fixes your team can apply immediately with minimal back-and-forth.
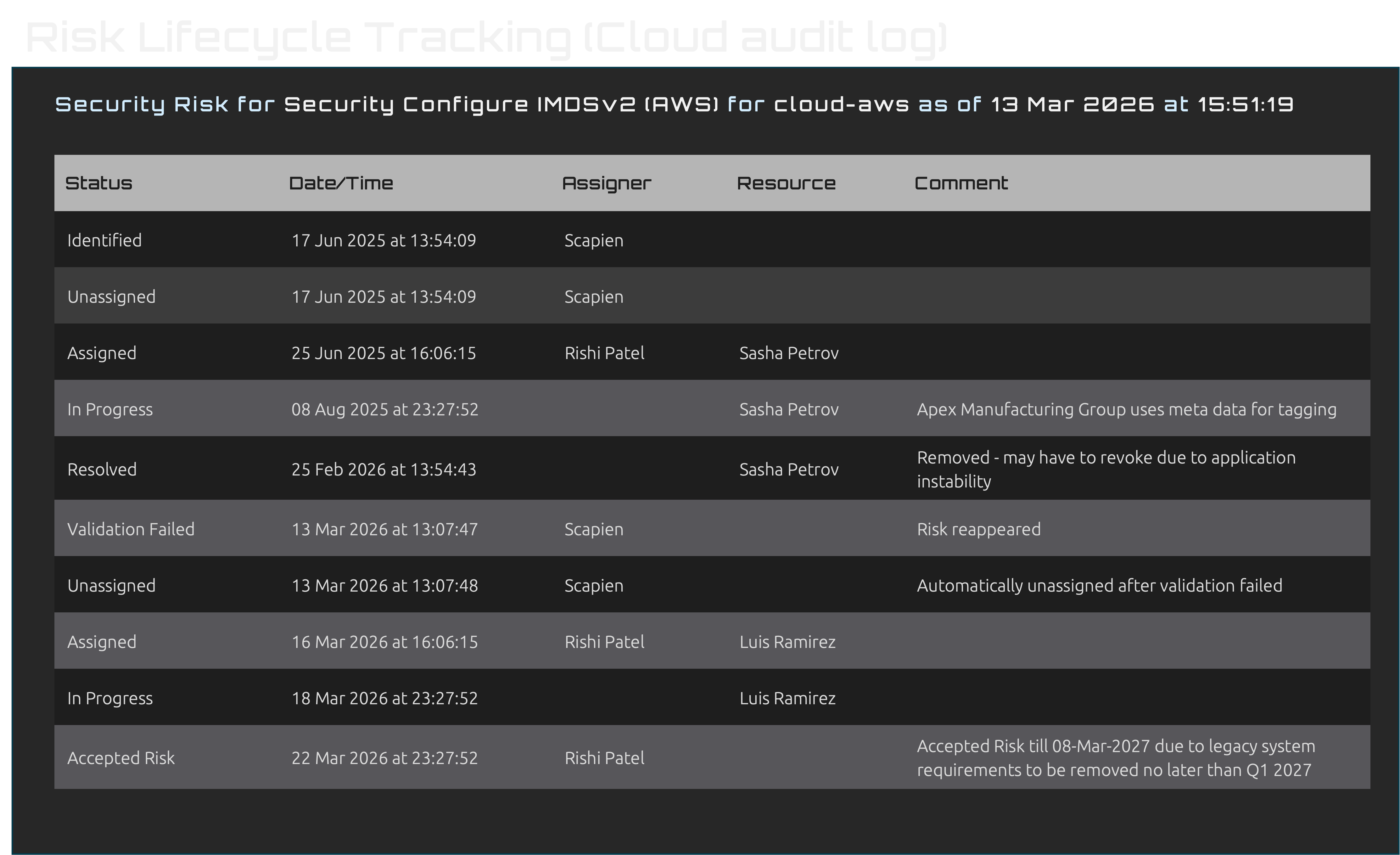
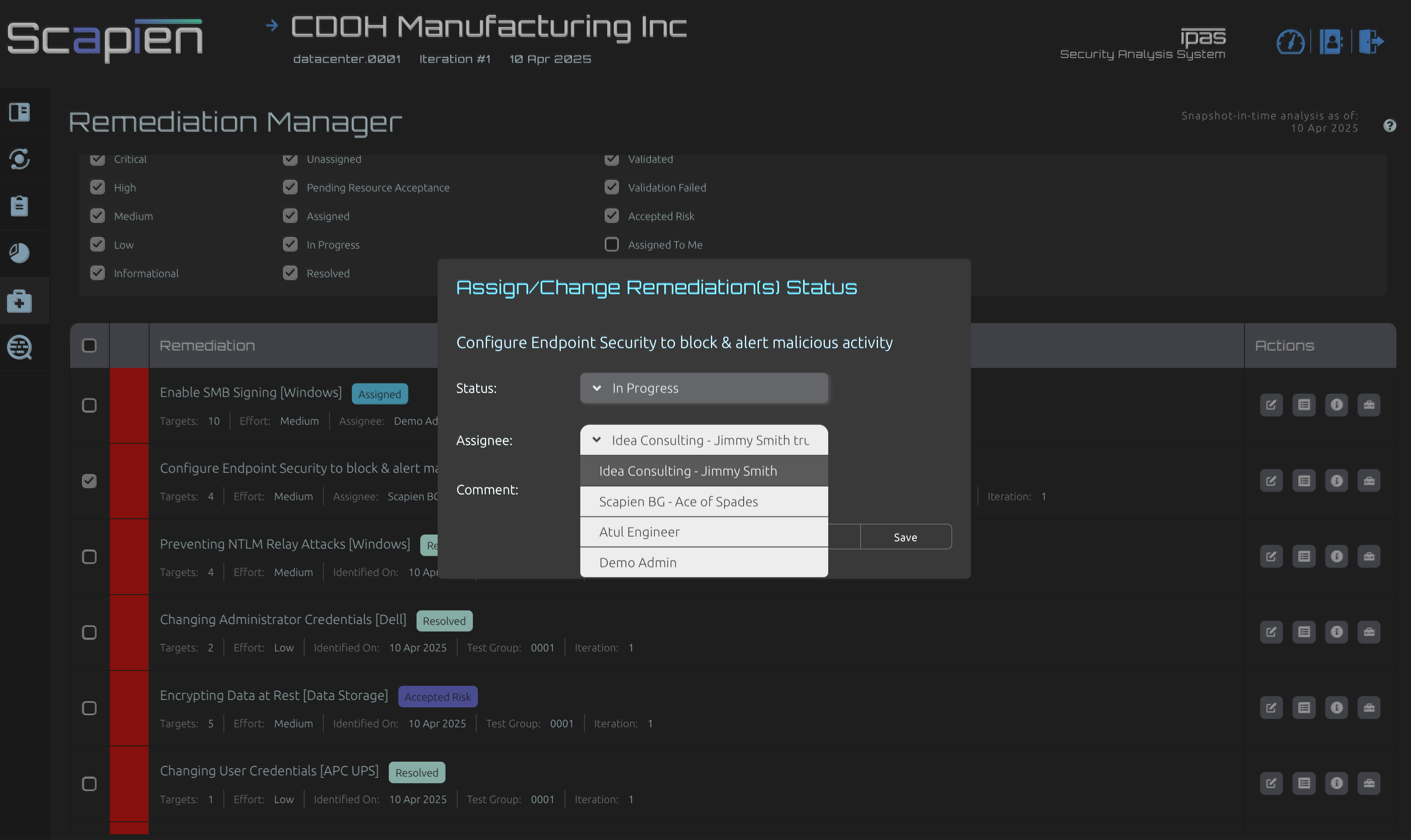
Validated security risks are published as Findings, each tied to assets, evidence, and remediation guidance. Before anything reaches the customer, results are validated and quality-checked so you receive a clean, efficient set you can act on immediately. Every finding moves through a tracked lifecycle — from discovery to assignment, remediation, retest, validation, and closure. The result is operational clarity and audit-ready state transitions captured in one system.
Walk through your environment, priorities, and where validated security risks may exist — without adding noise or unnecessary work.