Prove exploitability. Prioritize impact. Verify closure.
Prioritize What Matters: Proof of Risks, Not Alerts.
The CISO Blind Spot
You have alerts. You have tools. You have reporting
- Can you separate exploitable paths from theoretical exposure?
- Is remediation prioritized by attacker behavior, not generic severity scores?
- Can you prove critical risk stayed contained after change?
What Scapien Proves
Scapien shows how far an attacker can go, what the true blast radius looks like, and provides proof when those paths are actually closed.
- Confirms exploitable attacker paths, not just findings
- Validates whether lateral movement is actually contained
- Uses automation to remove repetition so human-led adversary testing can go deeper
- Verifies closure over time as environments change
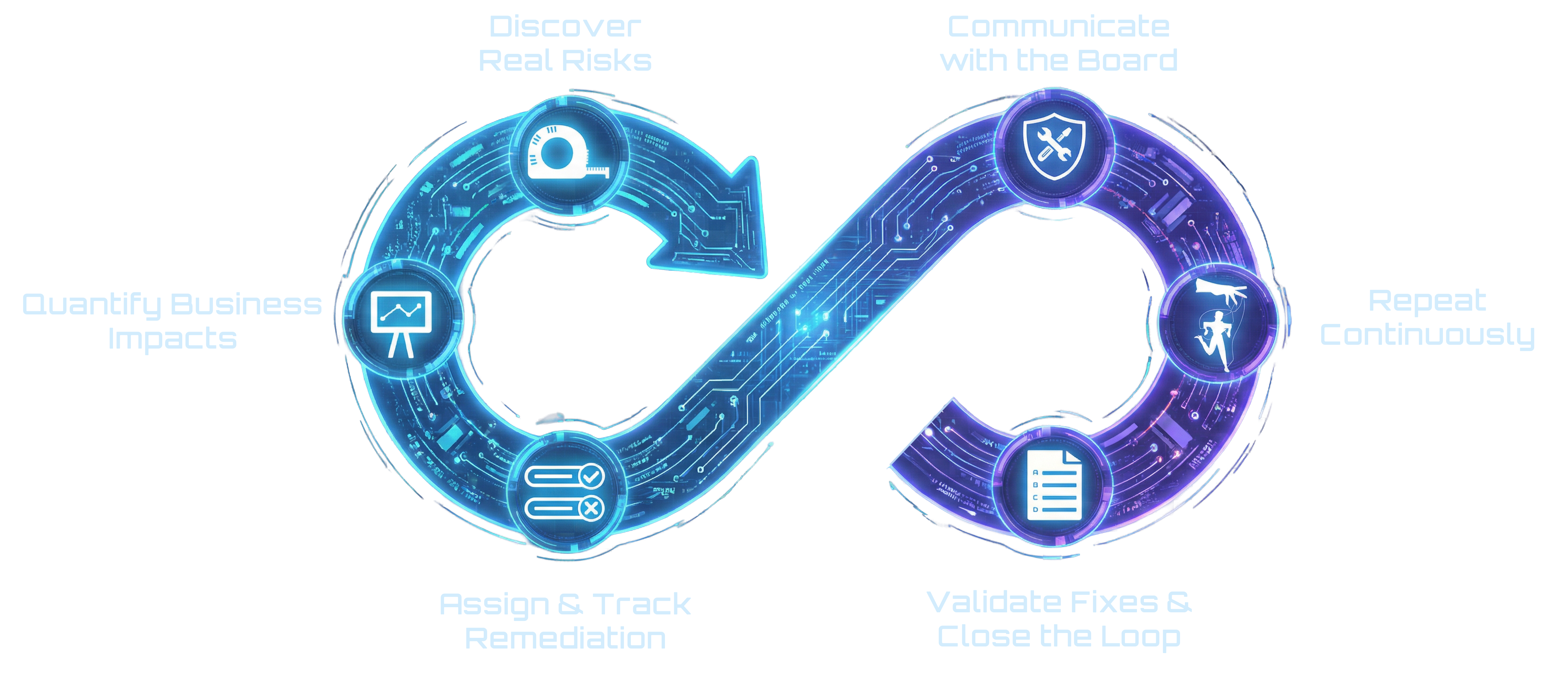
How it Works

1.Deploy
Deploy Scapien bots in your scoped environments. Starts as a black-box engagement by default.
2.Observe
Scapien mimics attacker 'dwell time' utilizing low-observability techniques and analyzing out of band telemetry to model your landscape.

3.Dynamic Attack
Our impact-weighted prioritization guides hybrid automated-human attack chains, validating vulnerabilities as real security risks.

4.Closure Assurance
Customers receive precise remediation steps, iPAS facilitates tracking, performs fix verification and counters drift through ongoing verification.
What Security Leaders Say
Before Scapien we were shooting into the dark, now we not only have the visibility into our vulnerabilities, but the ability to quickly remediate them.
Head of IT & Security, Manufacturing
With Scapien I know where my critical vulnerabilities are and can effectively communicate our security risks to my C-suite.
vCISO, Healthcare
I'm glad these guys are on our side; no other test even came close – I can sleep better knowing what I need to fix.
CIO, Retail
I've been purchasing tests & assessments for over a decade. This blows away anything we've ever seen – upset about all the money I've wasted in the past.
VP of Security, Travel
Understand the Difference
Case Study: Manufacturing & ICS Security
How validation changed prioritization and remediation effectiveness
Read the case study →How Security Leaders Think About Real Risk
Sign up for Scapien's Newsletter
Unsubscribe anytime